Can’t have Auth running using AD or LDAP.
1.Using AD.
My current configuration:
$config['auth_ad_check_certificates'] = false;
$config['auth_ad_check_certificates'] = 0;
$config['auth_ad_url'] = 'ldap://server.dc.domain.com:3268'; // you can add multiple servers
$config['auth_ad_port'] = 389;
$config['auth_ad_domain'] = 'domain.com';
$config['auth_ad_base_dn'] = 'DC=domain,DC=com'; // groups and users must be under this dn
#$config['auth_ad_binddn'] = 'CN=name sys. app,CN=Users,DC=domain,DC=com'; //base DN
$config['auth_ad_binduser'] = 'user';
$config['auth_ad_bindpassword'] = 'Password';
$config['auth_ad_timeout'] = 1;
$config['auth_ad_debug'] = false; //no need
$config['auth_ad_require_groupmembership'] = false; // false: allow all users to auth level 0
$config['auth_ad_user_filter'] = '(objectclass=user)';
$config['auth_ad_group_filter'] = '(objectClass=group)';
$config['auth_ad_global_read'] = 1;
$config['auth_api_local'] = true;
Bind username is [email protected]
Auth username is actually [email protected]
Application is allways trying to bind using user@‘auth_ad_base_dn’ that is wrong.
I tried to use https://github.com/librenms/librenms/compare/master…dGs-:add-option-adauth-as-userprincipalname
That actually works to do the bind for user because is using userprincipalname that is [email protected] (it means it has DC=country-code,DC=domain,DC=com).
But the problem is when is trying to get the attributes. Is searching for attribute in $config[‘auth_ad_base_dn’] but the user base_dn is DC=country-code,DC=domain,DC=com.
- Using LDAP.
My current configuration:
$config['auth_ldap_version'] = 3; # v2 or v3
$config['auth_ldap_server'] = 'ldap://server.dc.domain.com'; // Set server(s), space separated. Prefix with ldaps:// for ssl
$config['auth_ldap_port'] = 389; // 389 or 636 for ssl
$config['auth_ldap_starttls'] = false; // Enable TLS on port 389
#$config['auth_ldap_prefix'] = 'cn='; // prepended to usernames
#$config['auth_ldap_suffix'] = '';
#$config['auth_ldap_group'] = 'cn='; // generic group with level 0
$config['auth_ldap_groupbase'] = 'o=domain';
#$config['auth_ldap_groupmemberattr'] = 'ou=Employees'; // attribute to use to see if a user is a member of a group
#$config['auth_ldap_uid_attribute'] = 'extensionAttribute1'; // attribute for unique id
$config['auth_ldap_debug'] = true; // enable for verbose debug messages
$config['auth_ldap_userdn'] = true; // Uses a users full DN as the value of the member attribute in a group instead of member: username. (it’s member: uid=username,ou=groups,dc=domain,dc=com)
#$config['auth_ldap_userlist_filter'] = 'cn='; // Replace 'service=informatique' by your ldap filter to limit the number of responses if you have an ldap directory with thousand of users
$config['auth_ldap_wildcard_ou'] = true; // Search for user matching user name independently of OU set in auth_ldap_suffix. Useful if your users are in different OU. Bind username, if set, still user auth_ldap_suffix
$config['auth_ldap_binduser'] = 'CN=Libre NMS librnm1,ou=Resources,ou=company name,o=domain'; // will use auth_ldap_prefix and auth_ldap_suffix
$config['auth_ldap_binddn'] = 'CN=Libre NMS librnm1,ou=Resources,ou=company name,o=domain'; // overrides binduser
$config['auth_ldap_bindpassword'] = 'Password';
$config['auth_ldap_bindanonymous'] = FALSE;
$config['auth_ad_user_filter'] = 'uid';
$config['auth_ldap_groupmembertype'] = 'fulldn';
It’s always trying to bind using user and that’s it. Received the message “invalidDNSyntax”
If i’m trying to bind using fullDN i’m getting the message: “searchResDone(2) success (Search succeeded but at least one entry is incomplete.Found 1 Entries (0 Aliases), 30 Attributes, 30 Values. (ChainedResult=no))”
Then it’s again trying to bind using user and getting reply from LDAP server “invalidDNSyntax”
ldapsearch works fine using this command:
ldapsearch -x -b "o=domain" -H "ldap://server.dc.domain.com" -D "CN=Libre NMS librnm1,ou=Resources,ou=company name,o=domain" -W "(uid=user)"
I have a running application (limesurvey - opensource) that is working really well with LDAP.
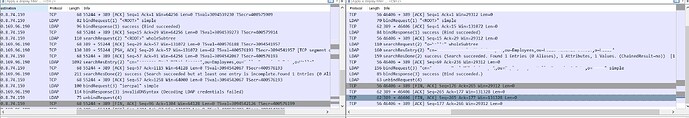
I used tcpdump to compare both query. Attached in the picture (left non working on librenms and right working).