I’m using Librenms and Oxidized on two different hosts. I could move Oxidized to the Librenms host if needed.
I guess I’m confused about how to secure Oxidized. Not that our switch configs have any real super secret information on them, but it’s nothing I really want hanging out there on our network.
I could do a reverse proxy with Nginx, but then Librenms doesn’t seem to be able to access it.
So how is everyone locking down access to Oxidized, but still having the data available to LibreNMS?
One way is to setup an nginx reverse proxy with two different server entries. Have one be ssl on 443 with auth for normal access, then setup a second on another port with no auth and only allow your librenms server access to that port.
Here is an example config /etc/nginx/conf.d/oxidized.conf
Thanks for sending that. I seem to be having an issue with nginx just being an proxy without any auth.
So right now I’m just using nginx as a straight proxy. No auth. I can get to the oxidized web page fine.
From the librenms box I’m able to curl the json information just fine:
[root@nms librenms]# curl http://oxidized.newberg.k12.or.us/node/show/10469s.newberg.k12.or.us?format=json
{“name”:“10469s.newberg.k12.or.us”,“full_name”:“10469s.newberg.k12.or.us”,“ip”:“10.56.96.6”,“group”:null,“model”:“JunOS”,“last”:{“start”:“2018-04-13 18:42:29 UTC”,“end”:“2018-04-13 18:42:41 UTC”,“status”:“success”,“time”:12.794961216},“vars”:null}[root@nms librenms]#
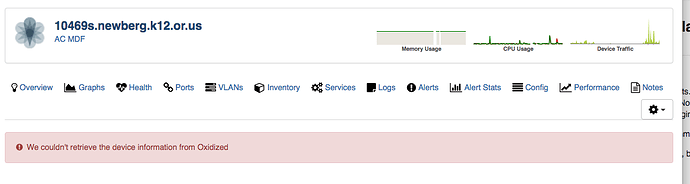
But when I access my config on the librenms webpage I get this:
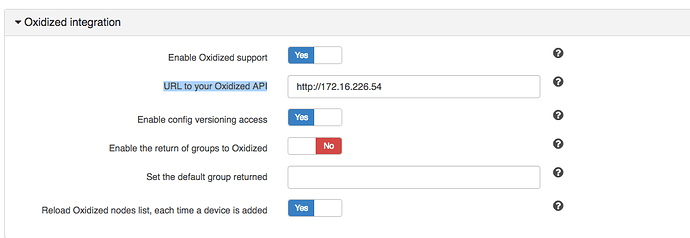
Here’s what my Librenms config for oxidized looks like:
Will you sanatize and post your nginx config and oxidized config in a pastebin?
Right now I have any auth commented out in nginx. Just trying to get this to work as a proxy first.
nginx config:
https://pastebin.com/KH6K5Nuf
oxidized config:
https://pastebin.com/LQi00MK3
I have that setup you are trying to do…if i understand what you are trying to do…
two diff hosts for oxidized and librenms
SSL 443 oxidize - for normal users. users are auth with the nginx ldap module
port 8888 oxidized - for api access; no auth
The config @theherodied provided is just for basic proxy which is good.
having another port for api access is just the same. here is a sample of mine. notice allow:
server {
listen xx.x.x.12:8888;
listen [x:x::12]:8888;
server_name _;
allow <librenms-ip>;
deny all;
location /oxidized {
#access_log /var/log/nginx/oxidized-access.log main;
#error_log /var/log/nginx/oxidized-error.log debug;
#auth_ldap "LDAP Authentication";
#auth_ldap_servers ldap_local;
proxy_pass http://localhost:9002/oxidized;
}
}
Did you follow the guide here:
https://docs.librenms.org/#Extensions/Oxidized/
Hope this is useful
dave
@davama, the config I provided does both as well. Top does auth with ssl, bottom does no auth with ssl.
I just limited access for the bottom with the firewall only. Edit: I added the allow/deny for added protection.
@theherodied whoops…i completely missed the auth part
your config looks good! what @mcparlandj needs
Who ever finds this, here’s the secure solution when using a apache reverse proxy and a subdirectory:
First, modify your oxidized config file to include your subdirectory.
Example for subdirectory ‘oxidized’ you’ll het
rest: 0.0.0.0:8888/oxidized
Then setup an apache reverse proxy like this
ProxyPass /oxidized http://localhost:8888/oxidized
ProxyPassReverse /oxidized http://localhost:8888/oxidized
RequestHeader set X-Forwarded-Proto "https"
<Location /oxidized>
AuthUserFile /var/www/default/ftp/www/.htpasswd
AuthName "Restricted Access"
AuthType Basic
Require ip 127.0.0.1
Require valid-user
</Location>
If librenms isn’t installed on the same server as oxidized, change the IP 127.0.0.1 to whatever the librenms server has.
Create the .htpasswd file with htpasswd command.
Don’t forget to update the librenms config URI for oxidized like
$config['oxidized']['url'] = 'http://127.0.0.1:8888/oxidized';
1 Like